Stop promoting “just trust me bro software” in the same title.
Anti-libre software, WhatsApp, bans us from proving its E2EE claims, any claims. It bans us from forking its source code, removing backdoors. It fails to include a libre software license text file, like AGPL, so they control it, not us. WhatsApp, anti-libre software, is a scam.
Wonder how they’d manage that as they both are E2EE.
A French and Dutch Joint Investigation Team (JIT) harvested more than 115 million supposedly encrypted messages from an estimated 60,000 users of EncroChat phones after infecting the handsets with a software “implant”.
Looks like they just hack the phone
https://en.m.wikipedia.org/wiki/EncroChat
So this sounds like the ANOM phone story with extra steps?
I get that they can “access” messages, but the headline feels misleading if it requires full access to the device.
It’s not that they’re breaking encryption or reading messages in transit, it’s more like they’re installing malware on specific devices so that they can look at your screen?
How does one get an “implant” onto a phone?
You implant it, duh.
Apparently what happened is that French police installed some of malware on the phones to read the messages, and this was now decided to be legal in the UK.
Damn, we’ll need those linux phones working soon.
Then they enforce the chipmakers to put backdoors in the chips themselves
I’d wager they already have
For x86 platforms it’s called Intel ME and AMD PSP.
What would that change?
You’d have enough control over the software that you can ensure nothing like this happens
Honestly mentioning Enchrochat together with other mainstream message clients is kind of misleading. The Enchrochat message client was also E2EE. However Enchrochat was also a company that sold their own mobile phones with a prorietary OS on it together with own sim cards and only those phones were able to connect to each other. And law enforcment had enough evidence that they sold those hardware in shady untracable ways similar to drugs. At that point there was no western government that didn’t want to help seizing their infrastructure and taking over their update services for example.
The bigger problem however for the general public is that certain politicians want to break encryption all together by forcing companies to implement backdoors on client side. This has been an ongoing discussion for 2 years in EU parliament and it has to stop: https://www.eff.org/deeplinks/2024/06/now-eu-council-should-finally-understand-no-one-wants-chat-control
With a warrant they could probably force signal/whatsapp to inject Malware into their apps to spy on users.
Don’t know how possible it is with signal and their reproducible builds. They would need to add this to the source code of the app.
Especially with Signal being open source. What stops the official Signal company from advertising another fork?
The server software is not open source.
Untrue. Stop spreading FUD: https://github.com/signalapp/Signal-Server
In that case: They started publishing code AGAIN.
The server soft has been available, then not, and apparently now again.
There’s a grain of truth in the claim: We don’t know for sure if the original open source version is actually running on the server.
They’ve said that they release the source code after it’s running in production:
sorry the source for one of our services was so far behind. We often don’t push source until we release things, and there were a few overlapping releases that happened in that period which made it awkward to push at any moment and put us behind. Additionally, we’ve seen a large increase in spam, and a reluctance to immediately publish the exact anti-spam measures we were responding with to a place where spammers could immediately see them combined with the above to cause this extreme delay.
https://github.com/signalapp/Signal-Android/issues/11101#issuecomment-815400676
Isn’t that true of all server side FOSS?
Yes. We just have to trust them. Or selfhost, which I’m doing with almost everything.
Man Signal would be the perfect messenger if it was defederated.
That’d be irrelevant, because as long as only the clients hold the keys (which we can verify, as those are not only open source but also are under our control, meaning we can check that the upstream open source version is installed and no private keys are being exchanged) there’s no way anyone can read the messages, except the owner of the private key.
Messages - yes, but there is also metadata. When ALL communication goes through the same servers, it becomes kind of a problem.
WhatsApp has MITM on the server side which is how Facebook scans your messages for targeted adverts. E2EE on WhatsApp was a fantasy the moment Facebook bought it
That is different than Signal which (unless they changed something with the profiles thing) was always P2P E2EE. You’re sending encrypted messages directly to the other persons phone, not to a server.
WhatsApp has MITM on the server side which is how Facebook scans your messages for targeted advert
You shouldn’t make claims like this when there is no evidence for it.
Signal which (unless they changed something with the profiles thing) was always P2P E2E
Signal has never been P2P.
Can someone explain how this is even possible with a service like Signal? I was under the impression that encrypted messages can’t be intercepted.
Extremely frustrating either way, I hate constantly having to manage different messaging services with different people and I’d really like to not have to add one more if signal becomes compromised.
It’s all client side. It even mentions infected clients.
Anything on the signal protocol could have an infected cilent be delivered, or backdoor server side by providing the wrong keys.
Facebook might comply. Would guess that Signal would refuse and would be hit by some absurd fee like 100mil a day for not complying and be forced to pull their services out of the UK.
Meta has all the power here. WhatsApp is ubiquitous in the EU. If they just shut it down, so many systems would be utterly fucked. They have to walk it back.
But I’m sure they don’t have the balls and don’t care, they’d just point at the gov and say “they made us do it!”.
UK… Not EU… Haven’t you heard of Brexit? They wouldn’t be allowed to do shit like that in the EU.
The EU is literally trying to do it right now: https://www.theverge.com/2024/6/19/24181214/eu-chat-control-law-propose-scanning-encrypted-messages-csam
afaik that law got snuffed out
For now, maybe.
Listen. I’m American. You can’t expect me to keep up with all the incredibly confusing regions and governments over there.
Upvoted you because I’m an euro and I still kinda agree with you. If Texas secedes, I have no idea what the implications are for legislation and court cases. It’s like half the size of the UK by population and 3x as big by area.
Sure everyone heard of brexit, but I’m sure many outside of the EU don’t know what it really is plus it took so damn long I honestly believed it might not even happen.
If Texas secedes, they can have fun on their own with their kangaroo court politics.
Truth be told, if Texas were to actually succeed in seceding, it would likely lead to a domino effect of other southern states following suit, and a royal fracturing of the US. How that plays out is anyone’s guess.
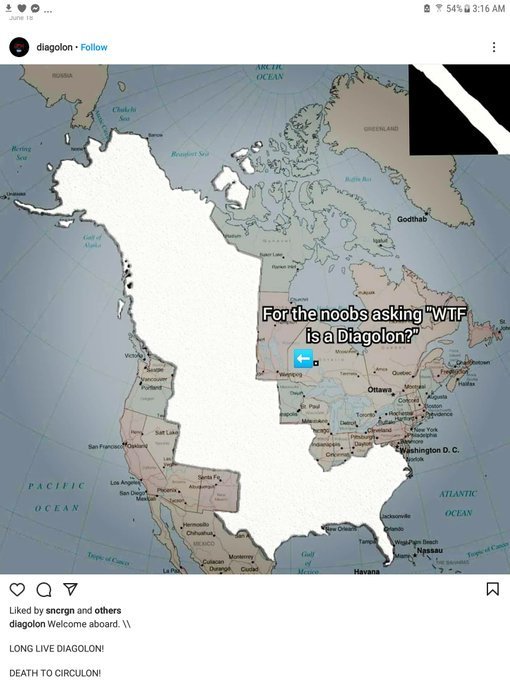
Kinda like this
If we have a war, will you be able to keep up then?
Nope.
Haha. I guess I also know only about the special children of America. Like Alabama xD















